Over 900 customers trust the best software for
information security, business continuity, and data privacy.








Modern and Efficient Data Protection Management
A tool should save you work, not create it.
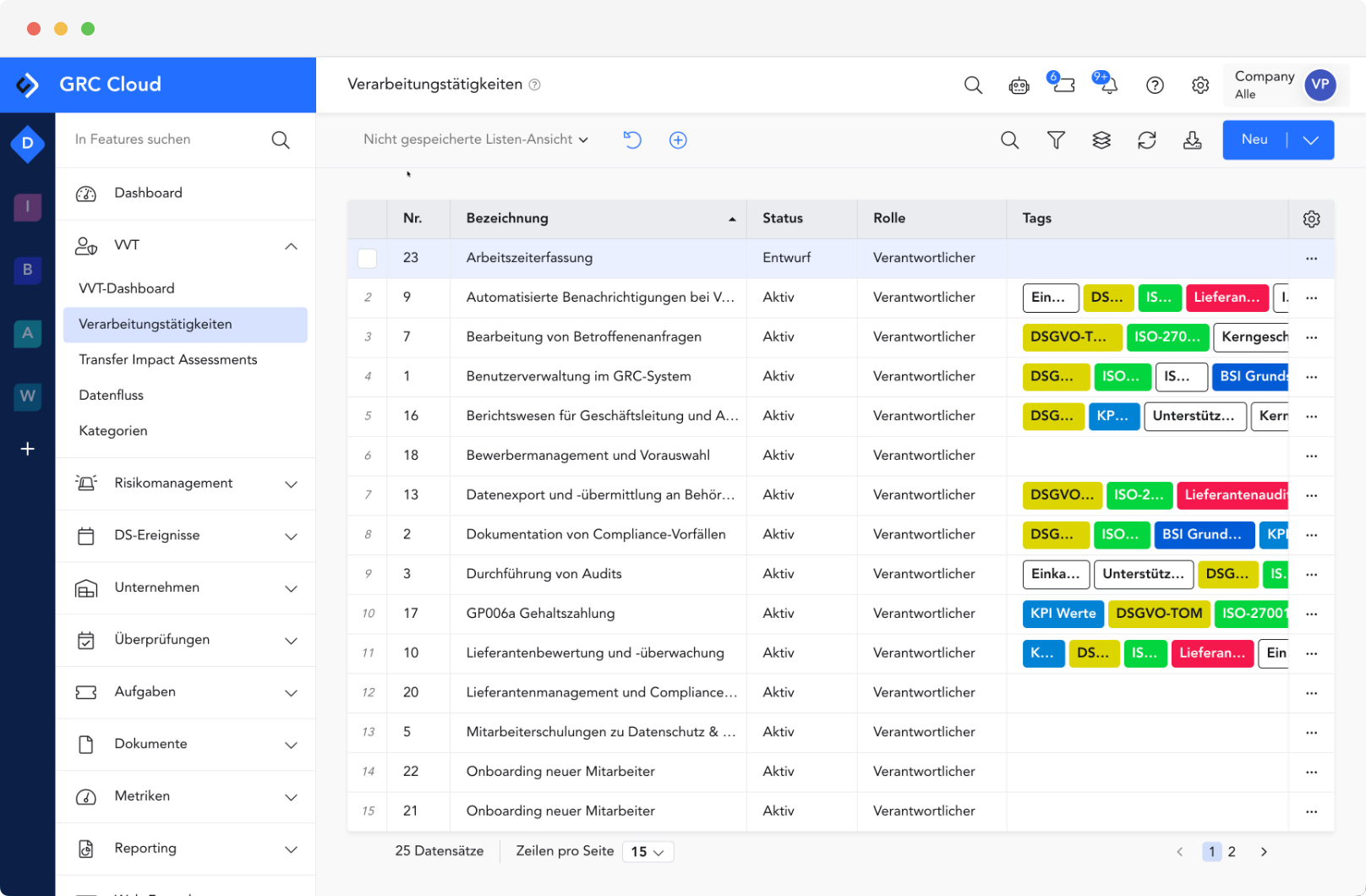
Dynamic Processing Directory (VVT)
Manage processing activities not as a static list, but as a dynamic system. Changes to processes or assets are automatically updated.
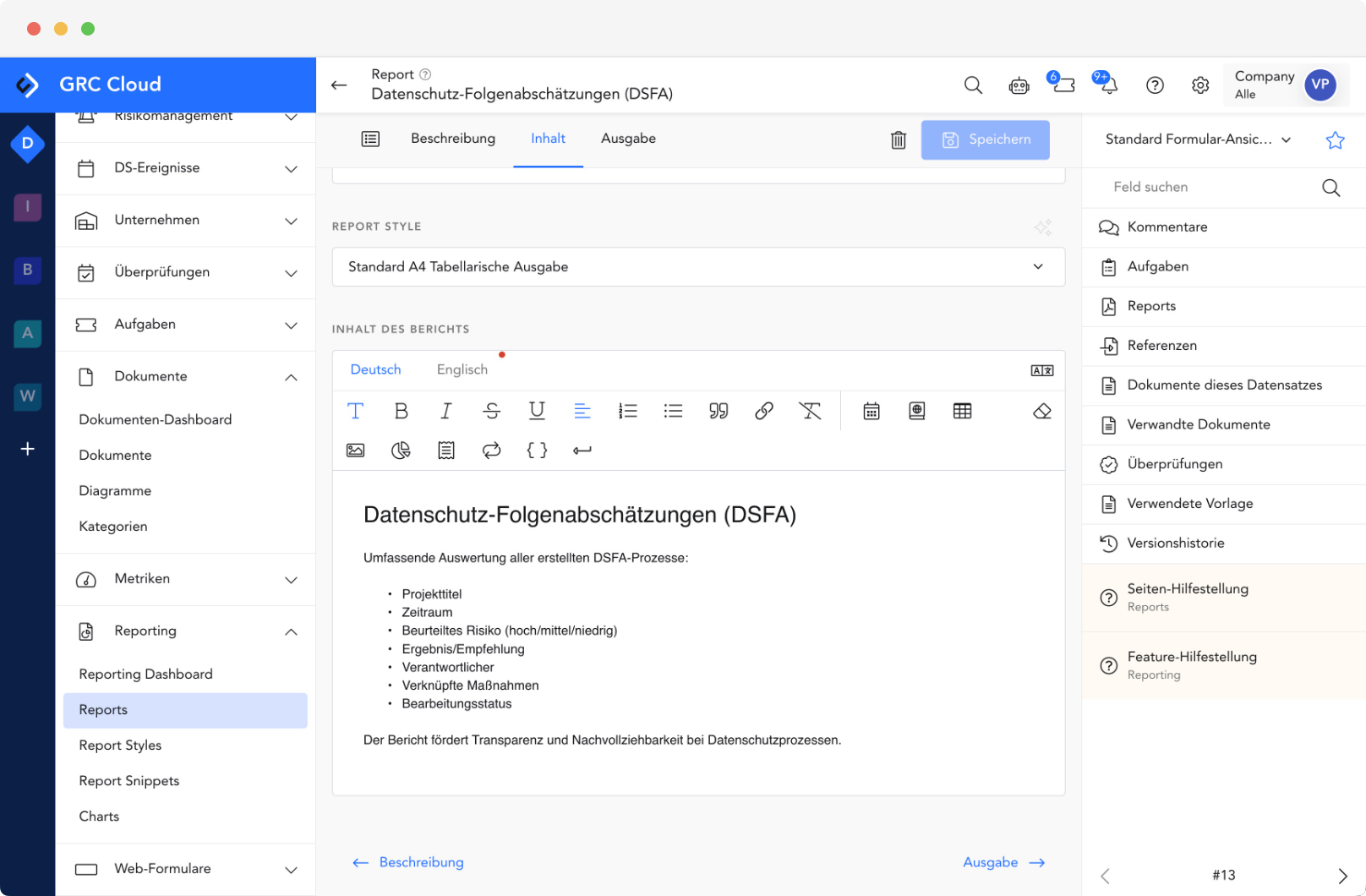
Data Privacy Impact Assessments (DPIA)
Conduct comprehensive assessments and visualize data flows directly within the system to identify risks to the rights and freedoms of data subjects at an early stage.
TOMs & Audit Documentation
Centralized recording, management, and complete documentation of implemented technical and organizational measures (TOMs), including customizable reports for regulatory authorities
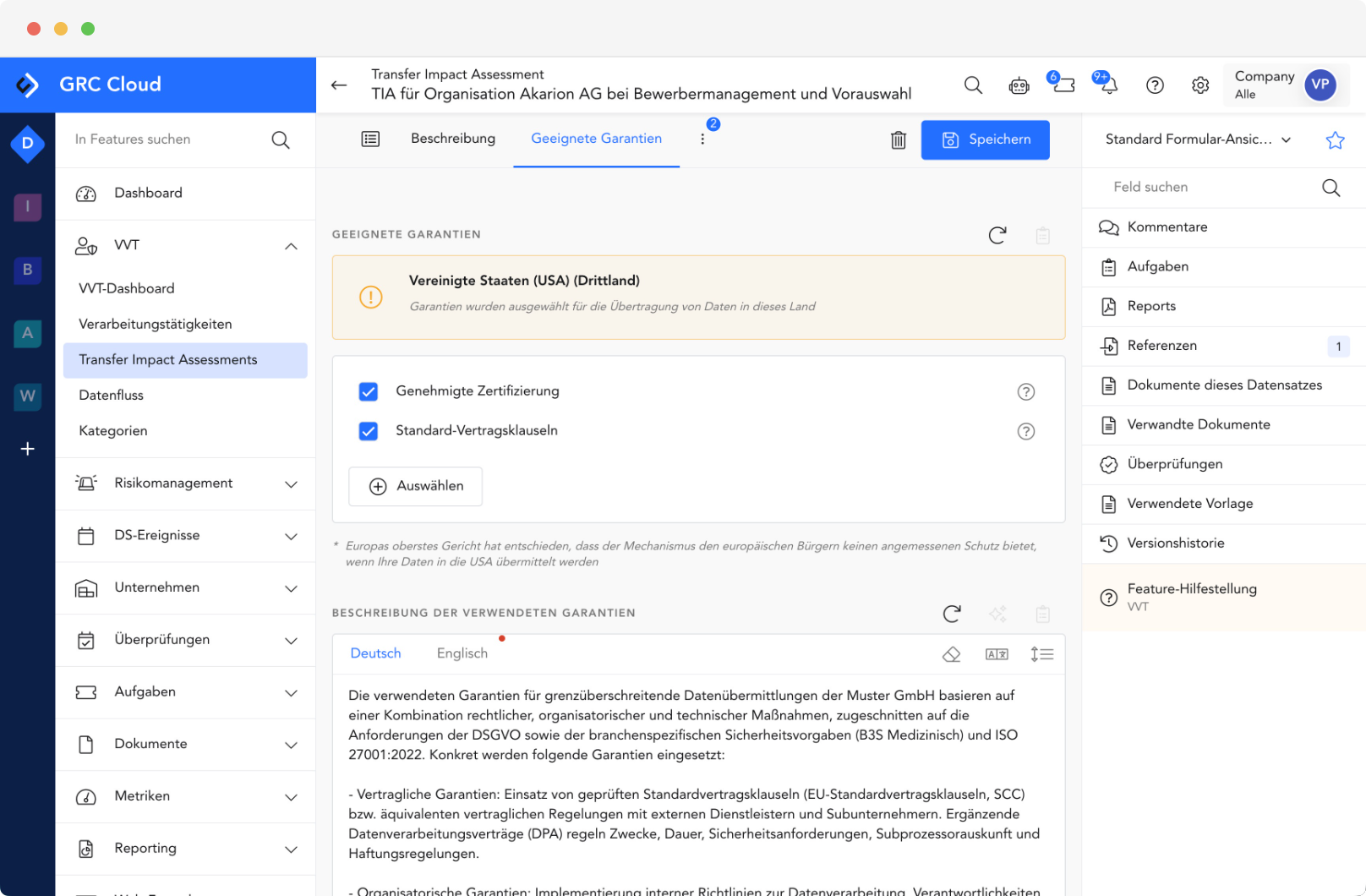
Transfer Impact Assessments (TIA)
Keep international data transfers under control. Review and document transfers to third countries securely and in compliance with the law.
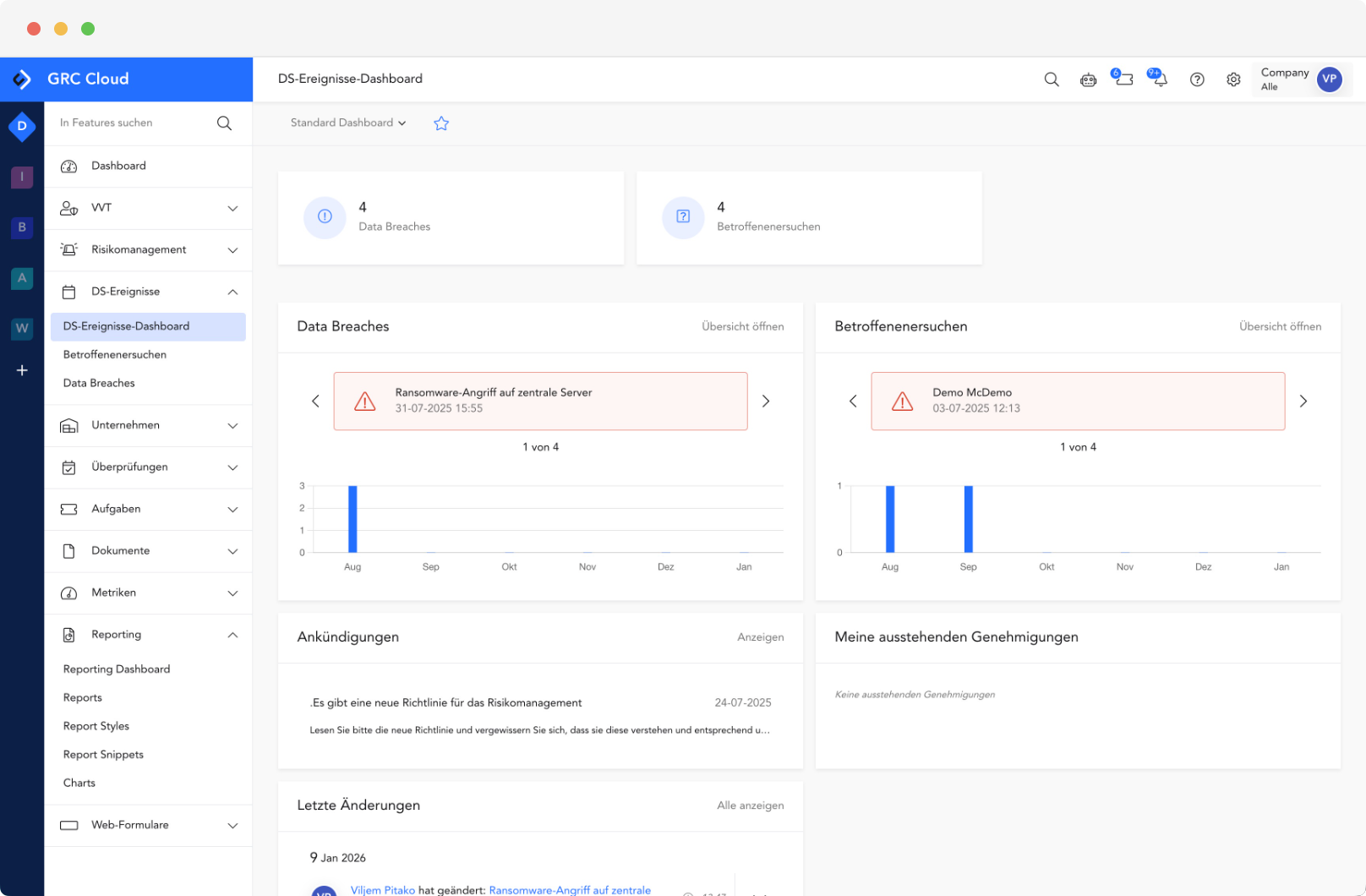
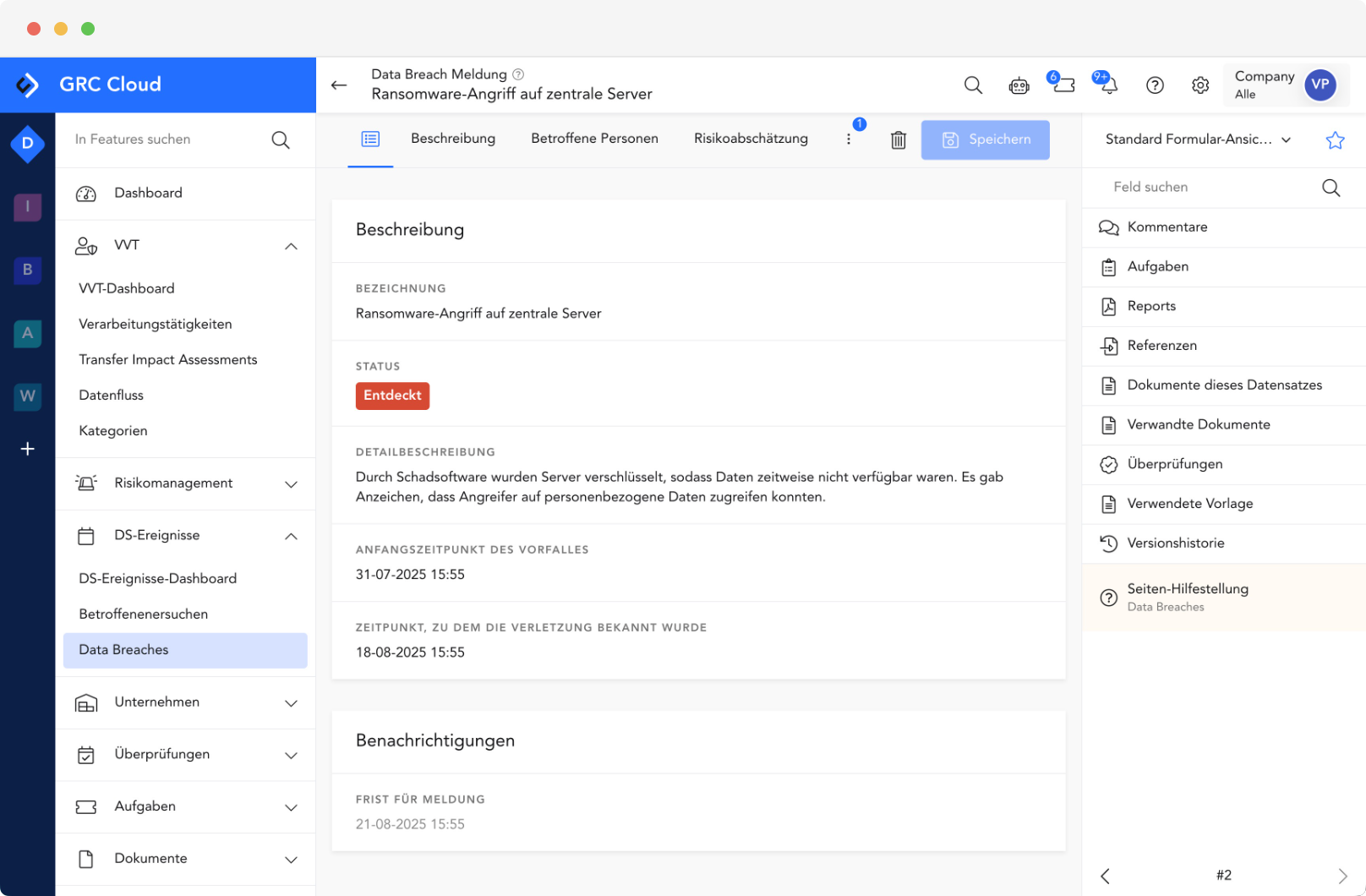
Data Breach Management
Respond immediately in the event of an incident. Our workflow guides you through the assessment process and monitors the critical 72-hour reporting deadline under the GDPR.
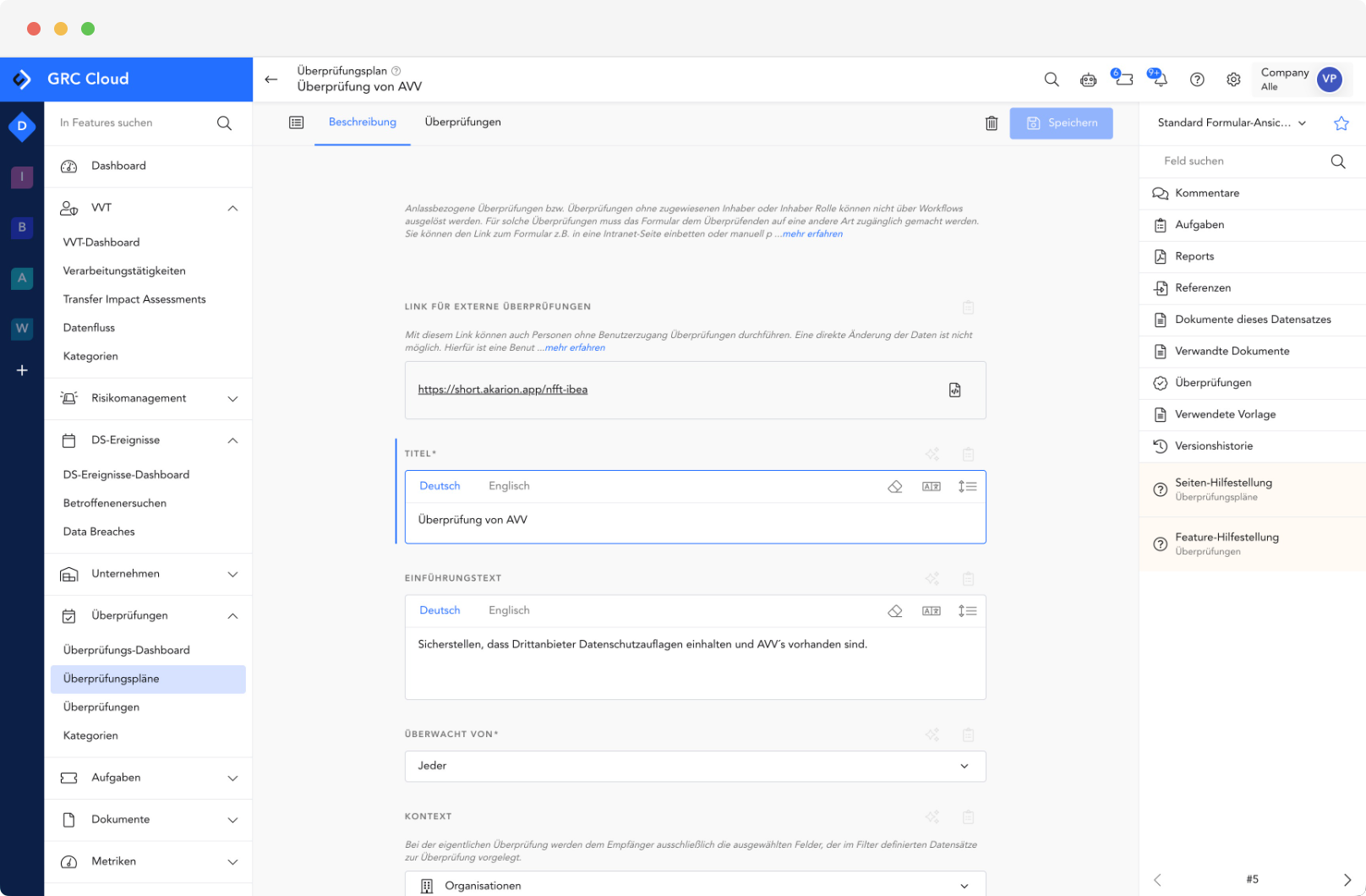
Data Processing (AVV)
Manage your data processors and service providers centrally. Keep track of contracts, audits, and risks in your supply chain at all times.
Perfect Synergies
Our modules are not standalone solutions. They share a central database, allowing data entered once—such as business processes, assets, TOMs, and much more—to be used across the other modules.
This avoids duplication of effort and provides a holistic view of your company’s resilience.
98% of our customers renew their licenses.

Frank Peter
Head of Data Privacy and Data Security
With the AKARION GRC Cloud, our consultants can effectively integrate data privacy and information security, thereby optimally meeting our clients’ needs. At the same time, we have become significantly more efficient. It’s a win-win situation for everyone involved.


Daniel Holzer
Managing Director
As the leading IT provider for municipalities in Upper Austria, we need a solution that is practical and intuitive to map the complex structures of public administration. The AKARION GRC Cloud helps us keep our municipalities’ documentation up to date and conduct annual audits efficiently.

Christian Bockrath
Information Security Officer
I have finally found software that allows me to conduct comprehensive risk analyses while taking both information security and data privacy into account. The resulting synergies can be fully leveraged.


Marco van Schoonderwaldt
Information Security Management Expert
The choice fell on the AKARION GRC Cloud—a decision that not only meets current needs but also supports future growth, particularly with regard to accessibility.


Theresa Steinmetz
Information Security Risk Manager
Data is our most valuable asset. It must be protected. Compared to the old Excel solution, the GRC Cloud saves us an enormous amount of time. I would estimate this at around 60 percent. In terms of usability, the improvement is actually 100 percent.


Alexander Dressler
Data Protection Manager
Data is our most valuable asset. It must be protected. Compared to the old Excel solution, the GRC Cloud saves us an enormous amount of time. I would estimate this at around 60 percent. In terms of usability, it’s actually 100 percent.

Tobias Schmidt
Security & Compliance
The comprehensive solution that AKARION offers through its GRC Cloud—covering data privacy, information security, risk management, and auditing—was exactly what we needed. The GRC Cloud serves as the central hub connecting our decentralized systems. This helps us immensely in locating the information we need.

FAQ: Data Protection Module
-
What is the purpose of the Akarion Data Protection Module?
The primary goal of our software is to ensure maximum efficiency throughout the entire DSMS lifecycle. The module helps you effectively manage data privacy risks, defend against attacks, and successfully guide your organization through audits. Our tool offers data privacy that flexibly scales with your business.
-
What are the core features of the Data Protection Module?
The module supports all core processes of a Data Protection Management System (DSMS):
-
Asset and risk management: Organization-wide modeling of processes and structures, as well as comprehensive asset and risk management.
-
Security Needs Assessment: It features automated security needs inheritance to ensure consistent security levels across all assets.
-
Control and measure management: You can create and maintain audit plans and control catalogs.
-
Incident Management: It offers systematic incident management for seamless tracking of security incidents.
-
Reporting: Data protection performance can be monitored through reporting and goal tracking using KPIs.
-
-
How does the Data Protection Module support employees in their daily work, and what about user acceptance of the solution?
User acceptance is very important to us. We prioritize a state-of-the-art user interface (UI) and optimal usability. Unlike rigid, complex tools, the Data Protection Module offers:
-
Intuitive workflows: Task, project, and workflow management ensure that measures and controls can be easily assigned and tracked.
-
Multilingual support: The platform supports automatic translation (multilingual), which significantly simplifies the global implementation of KDG requirements and collaboration within international teams.
-
Centralized overview: Customizable dashboards and reports provide every user—from the CISO to department heads—with the information they need—without Excel chaos.
-
-
Which common security standards and frameworks are supported?
The Akarion Data Protection Module is a DSMS software solution designed to support a wide range of international and national standards. These include:
-
GDPR
-
BSI IT-Grundschutz (BSI 200-2, 200-3, 200-4, ITGS Compendium, BSI C5)
-
NIS 2
-
ISO 27019, ISO 27701, ISO 22301
-
Sector-specific standards such as VDA ISA, PCI DSS, B3S Health/Energy
-
-
Is the Data Protection Module a standalone solution?
No, the module is an integral part of the Akarion Data Protection Module, the SaaS platform for integrated governance, risk, and compliance management. The platform combines DSMS, DSMS (data privacy), and BCMS (business continuity). Thanks to centralized data storage, you only need to enter processes, assets, and organizational units once and can use them across all relevant modules. This eliminates data redundancy and ensures maximum efficiency.
-
Why use software for data privacy?
Specialized software such as the Akarion Data Privacy Module centralizes and automates data privacy management. It provides a unified platform for policies, risk assessments, training, and the management of corrective actions. This reduces manual effort, ensures auditability, and improves the efficiency of the security strategy.
-
Why do manual DSMS approaches (Excel/file servers) often fail in the long run?
Getting started with Excel seems simple, but the complexity grows exponentially:
- Missing link: If a server (asset) fails, Excel does not automatically show which business processes are affected and which KDG reporting requirement is triggered.
- "Chinese whispers" with evidence: Before audits, hundreds of screenshots and documents must be collected via email from specialist departments. This is error-prone and extremely time-consuming.
- No historical data: Excel only shows the current status. However, an auditor might ask, “Show me how this risk has evolved over the past 12 months”—which is virtually impossible to do manually.
-
Why use software for data protection management systems?
DSMS software streamlines the complex requirements of a DSMS (such as the GDPR or BDSG). Their solution centralizes all documents, automates risk analysis and action tracking, and ensures that you remain audit-compliant at all times.
-
How does the Data Protection Module represent an "integrated management system"?
The strength of the Data Protection Module lies in its ability to link data to avoid redundancies:
- Multi-Compliance Mapping: You implement a measure (e.g., "two-factor authentication"). The software automatically links this single piece of evidence to the requirements of the GDPR (Article 8.5), BDSG (Section 4.A8), and NIS 2. Do the work once, reap the benefits many times over.
- Centralized Asset Inventory: All assets (servers, applications, service providers, processes) are recorded centrally once and serve as the basis for risk analyses, Business Continuity Management (BCM), and data privacy.
- Audit-proof workflows: Every risk approval, every acknowledgment of a policy, and every completion of a control task is logged with a timestamp and user, and cannot be altered.
-
What is the structure of a DSMS?
A DSMS is typically structured according to the PDCA cycle (Plan-Do-Check-Act):
- Plan: Define the guidelines and objectives.
- Do (Execute): Implementing the measures.
- Check (Review): Monitoring effectiveness and conducting audits.
- Act (Improve): Continuous optimization.
One platform, all solutions
Expand the data privacy module with modules for BCM, data privacy, and auditing. The path to an integrated management system has never been easier.
Frequently Asked Questions About the GDPR, BDSG, and KDG
-
What is the GDPR?
ISO/IEC 27001 is a globally recognized standard that establishes requirements for an ISMS. It provides organizations with a framework for systematically managing and protecting information and includes a list of recommended security measures.
-
Which companies are affected by the GDPR?
The GDPR applies across all industries and can be implemented by any organization that wishes to demonstrate its commitment to protecting data. It is particularly relevant for companies that must meet stringent compliance requirements (e.g., IT service providers, the financial sector).
-
Why use software to implement the GDPR?
Implementing the GDPR involves a great deal of documentation and process management. Software such as our Akarion Data Protection Module supports you by providing the required documentation, simplifying the risk assessment, and centrally and systematically managing all evidence of compliance.
-
How can a company become GDPR-certified?
Certification typically follows these steps:
- Planning and setting up the DSMS (with the support of software).
- Implementation of the necessary measures.
- Internal audit to verify effectiveness.
- External audit by an accredited certification body (often in two phases: Stage 1 and Stage 2).
-
How can software help me with a GDPR audit?
Their software ensures that all policies, protocols, risk analyses, and documentation (e.g., training completed and measures implemented) are complete, up-to-date, and easily accessible. This significantly reduces the time required for audit preparation and allows the auditor to quickly assess compliance with the standard.
-
What is the BDSG?
The BDSG is a methodology developed by the Federal Office for Information Security (BSI) to ensure an appropriate and secure level of protection for organizations' IT systems and information. It is based on modules with specific security requirements.
-
What are the protection objectives of the BDSG?
The three core data protection objectives are identical to those of the GDPR: confidentiality (protection against unauthorized access), integrity (protection against unauthorized modification), and availability (ensuring functionality).
-
What is the difference between the BDSG and the GDPR?
Attribute
GDPR
BDSG
Approach
Risk-based (The company decides which measures to implement based on the risk analysis).
Standardized (Provides concrete, comprehensive catalogs of measures that define the "basic level of protection").
Focus
International standard, management system.
German standard, very detailed technical and organizational components.
Certification
GDPR certificate (recognized worldwide).
BDSG certificate (primarily relevant in Germany).









